Endpoint Protection

How Secure is your Cloud data
With employees working remotely at higher rates, business data is increasingly at risk. IT administrators...
Insider Threat Prevention Guide
In a perfect world, trust would never be violated. Cyber defenses would be impregnable. No employee would...
Sophos 2022 Threat Report
Interrelated threats target an interdependent world. We believe that shifting the timescale of attack...
Cybersecurity Governance for Small and Medium Businesses
Building a foundation to enable cybersecurity governance is key. The cyber threat landscape is constantly...
6-Step Cybersecurity Starter Guide for SMBs
Computers and the internet bring many benefits to small businesses, but this technology is not without...
BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...
Escape the Ransomware Maze
Ransomware is an ever-evolving form of malware designed to steal business-critical data and then sell...
The Complete Guide to Enterprise Ransomware Protection
The SentinelOne Complete Ransomware Guide will help you understand, plan for, respond to and protect...

Building the foundation of a mature threat hunting program
Many organizations, especially large global enterprises, don't always have the best visibility into how...
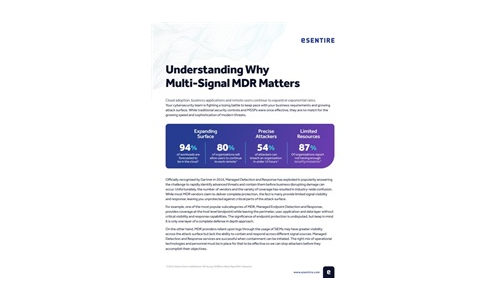
Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...
Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...

Multi-Vector Protection
Educating users is an undeniably effective way to protect them from phishing and other malware, but it...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.