Endpoint Protection

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
Escape the Ransomware Maze
Ransomware is an ever-evolving form of malware designed to steal business-critical data and then sell...

Realizing The Devops Vision In Embedded Systems
Markets demand ever more complex systems and faster development cycles. Meanwhile, there is a shortage...
The Complete Guide to Enterprise Ransomware Protection
The SentinelOne Complete Ransomware Guide will help you understand, plan for, respond to and protect...
Social Engineering Handbook: How to Take the Right Action
The aim of this handbook is to help introduce social engineering and its risks to every employee in the...
Insider Threat Prevention Guide
In a perfect world, trust would never be violated. Cyber defenses would be impregnable. No employee would...
6-Step Cybersecurity Starter Guide for SMBs
Computers and the internet bring many benefits to small businesses, but this technology is not without...
Building Your MSP Security Offerings
As a managed service provider (MSP), your customers already expect you to keep their networks secure....
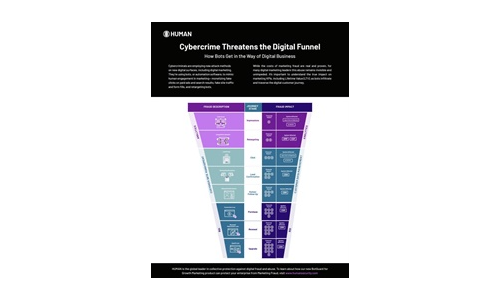
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...
How to protect your business from ransomware
Read this guide to gain an insight into how you can take proactive steps to keep your company's files...
Sophos 2022 Threat Report
Interrelated threats target an interdependent world. We believe that shifting the timescale of attack...

5 Benefits of Partnering with Webroot
While cyberattacks continue to evolve in volume, organization, and sophistication, security technology...

Enhancing Microsoft Security with HelpSystems Email Security
Learn how HelpSystems Email Security can enhance Microsoft 365. Microsoft 365 offers tiers of security...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

