Cloud Security

6 Lessons for Cybersecurity Leaders
The state of security is highly adrenalized these days — more so than usual. Years into the deadly...
Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...
How a modern frontend can transform your ecommerce business
Our Whitepaper reviews 5 ways JAMstack and a modern CDN edge cloud platform will boost your ecommerce...
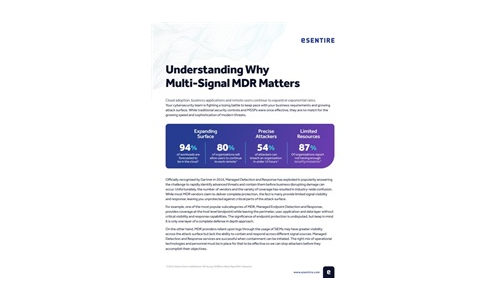
Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...

15 Ways Your Website is Under Attack
Web applications are the home of your business on the internet. The functionality within your website,...

Why Security Needs An Application-Centric Lens
An application-centric view of security should be based on four critical security capabilities. We discuss...

Defending Ukraine: Early Lessons from the Cyber War
The latest findings in our ongoing threat intelligence efforts in the war between Russia and Ukraine,...

Raising the Bar for Web App and API Security
Most Web Application and API Security Isn't Enough Securing the web applications and APIs that underpin...
The Five Nastiest Security Mistakes Exposing Public Cloud Infrastructure
Public cloud infrastructure has become a critical asset to enterprises that compete on innovation. Protecting...
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.