Latest Whitepapers
Architecting the Zero Trust Enterprise
Zero Trust is a strategic approach to cybersecurity that secures an organization by eliminating implicit...
The Increase in Mobile Wallet Adoption Impacts the Need for Security
The use of mobile payments is on the rise! According to industry data, mobile wallets are used by more...
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...
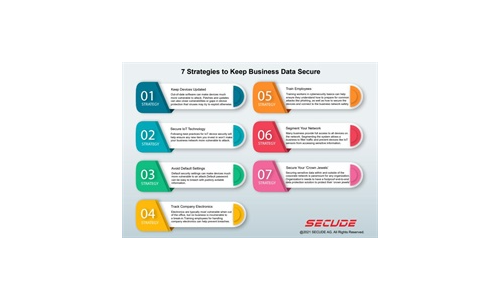
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
A Guide for SMBs: Can I really become “less hackable”?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...
Ransomware Case Studies
Ransomware is a simple name for a complex collection of security threats. Attacks can be short and brutal,...

The Future of Cybersecurity For Today’s Cloud- and Mobile-First World
Today, there's a sharp focus on embracing zero trust as the future of cybersecurity. With apps, users,...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...
12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...
Inside Complex Ransomware Operations and the Ransomware Economy
Ransomware operators have steadily become more sophisticated and more aligned with nation-state actors,...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.