Latest Whitepapers

Vulnerability and Patch Management
Patching vulnerabilities is a constant battle for organizations, which is why threat actors frequently...
Navigating the Cloud: Key factors for long term success
The cloud is not only here to stay, its impact is growing. As cloud-based solutions and capabilities...

15 Ways Your Website is Under Attack
Web applications are the home of your business on the internet. The functionality within your website,...
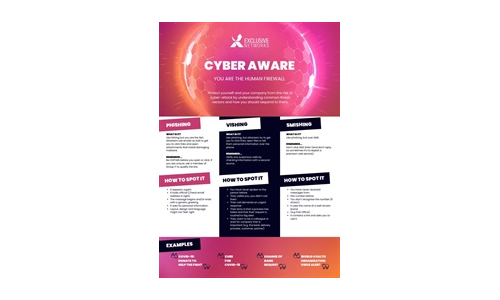
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
How to protect your business from ransomware
Read this guide to gain an insight into how you can take proactive steps to keep your company's files...

How Secure is your Cloud data
With employees working remotely at higher rates, business data is increasingly at risk. IT administrators...

A Tiered Framework For Cyber Threat Levels
If you're a “Trekkie” you know that “shields” refer to advanced technology to protect starships,...

Enhancing Microsoft Security with HelpSystems Email Security
Learn how HelpSystems Email Security can enhance Microsoft 365. Microsoft 365 offers tiers of security...
How a modern frontend can transform your ecommerce business
Our Whitepaper reviews 5 ways JAMstack and a modern CDN edge cloud platform will boost your ecommerce...
2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

CIO Essential Guidance: CISO Security Threat landscape
After a year that saw the largest and fastest transformation in work patterns in history, security teams...

Defending Ukraine: Early Lessons from the Cyber War
The latest findings in our ongoing threat intelligence efforts in the war between Russia and Ukraine,...
Using MITRE ATT&CK™ in Threat Hunting and Detection
Threat hunting is the process of proactively searching for malware or attackers that reside on your network...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.