Latest Whitepapers

The Top Questions to Ask in Your SASE RFP
Moving to a cloud-delivered architecture can be daunting. It is essential to find a SASE provider who...
NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...

Vulnerability and Patch Management
Patching vulnerabilities is a constant battle for organizations, which is why threat actors frequently...
The Five Nastiest Security Mistakes Exposing Public Cloud Infrastructure
Public cloud infrastructure has become a critical asset to enterprises that compete on innovation. Protecting...
An Overview of Cato Data Loss Prevention (DLP)
ata is the most valuable asset a modern enterprise has. The evolving threat landscape and shift to cloud...
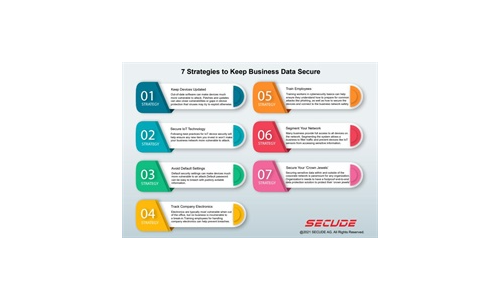
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
What is the Cost of a Misdirected Email?
The average number of misdirected emails is almost always higher than IT leaders estimate, making it...
Modern Networking for the Borderless Enterprise
5 Ways Top Organizations Are Optimising Networking at the Edge. Enterprises are growing more dispersed...
Essential How-To Guide: Prevent Accidental Emailing
NO ORGANIZATION IS IMMUNE TO HUMAN ERROR In this e-book you'll get a closer look at data breaches and...

A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...

Lay the Foundation for Zero Trust
Zero Trust has been a topic of discussion in the Federal Government for some time. However, the approach...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.