Firewall
Cloud Security Report 2022
Cloud adoption continues to permeate throughout organizations as they embrace agile software development....

Redefining the Role of the RTOS
The world of embedded systems is undergoing a profound evolution. Once isolated and purpose-built, embedded...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...
The Pitfalls of SASE Vendor Selection: Features vs. Strategic Outcomes
After speaking with 1000s of IT pros, we've learned that success with SASE is only achieved when it meets...
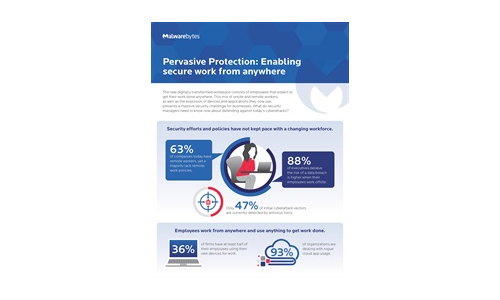
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
Collective Defense: A radar-like view of cyber threats
IronNet is committed to answering the World Economic Forum's call to action for collaborative cyber defense....
Remote Access Security checklist for every IT admin
Keep your remote workforce secure and productive. Find everything you need to ensure remote workforce...
Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...

The State of Security within eCommerce
2020 is a year unlike any other. Among the many effects of the global pandemic is the significant increase...
Public Sector Cloud Journey
As the government continues to move workloads to the cloud, many agencies are struggling to automate...

AI Driven Threat Defense The Next Frontier in Cybersecurity
It's undeniable that the landscape of modern cybersecurity has evolved dramatically—and at a rapid...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.