Data Security
5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...
Proofpoint Information and Cloud Security Platform
The Proofpoint Information and Cloud Security platform combines many of our products to address secure...

5 Tips for Managing Third-Party Risk
Across industries and around the world, executives remain preoccupied with digital transformation. According...
Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...
Open Channels, Hidden Threats
How Communication and Social Media Tools Are Changing the Insider Risk Equation for Compliance, IT and...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

Risk-Adaptive Data Security: The Behavior-Based Approach
This eBook addresses the challenge with DLP of either applying restrictive policies which slow down the...

UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...
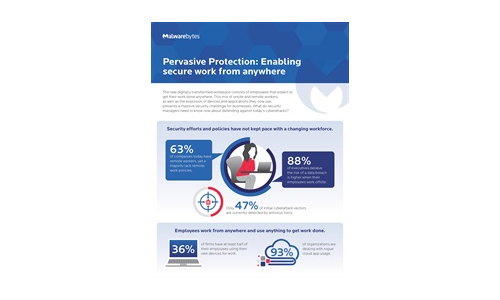
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

2021 Data Risk Report - Manufacturing
Our 2021 Manufacturing Data Risk Report focuses on the growing cybersecurity threats facing industrial...

6 Lessons from SASE Innovators
How Leading Organizations Are Getting Ahead with Prisma SASE Enterprises have traditionally taken a hardware-based...
Modern Networking for the Borderless Enterprise
5 Ways Top Organizations Are Optimising Networking at the Edge. Enterprises are growing more dispersed...
Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...

A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

