Data Security
The Top 10 Biggest and Boldest Insider Threats
Over the last two years alone, insider security incidents have jumped 47%, with the average cost per...

UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...

Protecting your content against cyber threats and data loss
How the Content Cloud safeguards your most valuable information Your business runs on content — but...

PCI Compliance Best Practices
The Payment Card Industry Data Security Standard (PCI DSS) has been in place since 2004, with the latest...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...

5 Tips for Managing Third-Party Risk
Across industries and around the world, executives remain preoccupied with digital transformation. According...

Cloud Adoption and Risk Report
The recent work from home mandate has dramatically changed how we live and work. Organisations are getting...
2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...

Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...
Privileged Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft headlines are the number one attack...
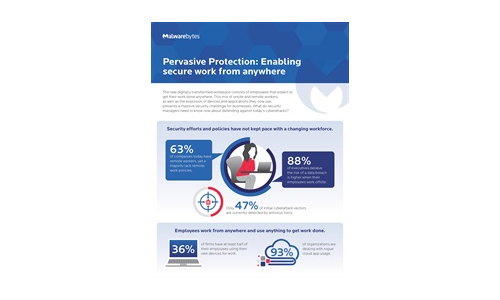
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
10 Key Questions to Include in Your Vendor Security Questionnaires
Today's perilous cyber world requires you to carefully check your vendors' security posture – typically...

The Passwordless Future Report
Every company has to become a technology company in order to survive and thrive in today's competitive...
Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme Insider threats can...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

