Data Loss Prevention (DLP)

6 Lessons from SASE Innovators
How Leading Organizations Are Getting Ahead with Prisma SASE Enterprises have traditionally taken a hardware-based...
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...

Three Reasons to Move from Legacy DLP
Changing your data loss prevention (DLP) solution is a major transition that can feel overwhelming. But...
Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...

The 10 Tenets of an Effective SASE Solution
As cloud adoption grows, cloud-enabled organizations are experiencing an influx of new security requirements....
Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme Insider threats can...
2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...

Redefining Data Loss Prevention (DLP)
Data doesn't move itself. People—whether they are negligent, compromised or malicious—move data in...
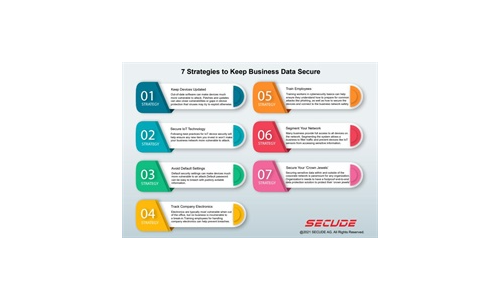
7 Strategies to Keep Business Data Secure
Read our simple infographic which headlines seven strategies to keep your business data secure. ...
Modern Networking for the Borderless Enterprise
5 Ways Top Organizations Are Optimising Networking at the Edge. Enterprises are growing more dispersed...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.