Network Security

Lay the Foundation for Zero Trust
Zero Trust has been a topic of discussion in the Federal Government for some time. However, the approach...

15 Ways Your Website is Under Attack
Web applications are the home of your business on the internet. The functionality within your website,...
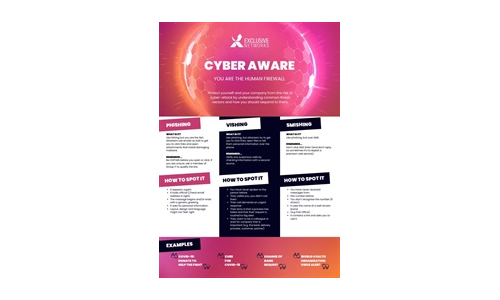
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
The Pitfalls of SASE Vendor Selection: Features vs. Strategic Outcomes
After speaking with 1000s of IT pros, we've learned that success with SASE is only achieved when it meets...

2022 Cyberthreat Defense Report
Interested in strengthening your cybersecurity strategy? Each year, CyberEdge provides a comprehensive...

10 Security Tips for Businesses
SECURITY THAT PROTECTS YOUR BUDGET Vanishing budgets, reckless users, infected machines, unpatched software...
Remote Access Security checklist for every IT admin
Keep your remote workforce secure and productive. Find everything you need to ensure remote workforce...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...

6 Lessons from SASE Innovators
How Leading Organizations Are Getting Ahead with Prisma SASE Enterprises have traditionally taken a hardware-based...
Alphabet Soup: Making Sense of XDR, EDR, NDR, and SIEM
XDR, EDR, NDR, and SIEM. They are among the most prominent acronyms in cybersecurity. But what do they...
The Three Keys to Secure and Successful Cloud Migrations
To make cloud transformations as efficient and successful as possible, companies must remain secure and...
Open Channels, Hidden Threats
How Communication and Social Media Tools Are Changing the Insider Risk Equation for Compliance, IT and...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.