Email Security

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...
5 Uncomfortable Truths About Phishing Defense
When over 90% of breaches start as phishing emails threats that email gateways miss and other defenses...
The CISO's Guide to Ransomware Prevention
Ransomware attacks have transformed the cyber attack landscape. These sophisticated and persistent threats...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

Secure Email Gateway: Buyer’s Guide
Protecting your organization against email-borne threats is only becoming more difficult as attackers...
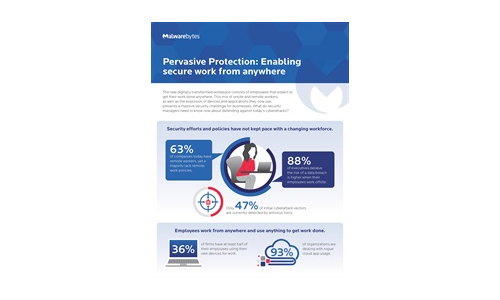
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...

A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...
Drive Real Behaviour Change
Cybersecurity awareness training is one of the most important things you can do to secure your organisation....
Privileged Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft headlines are the number one attack...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.