Confidentiality

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
The Complete Guide to Enterprise Ransomware Protection
The SentinelOne Complete Ransomware Guide will help you understand, plan for, respond to and protect...
CMMC Compliance Guide
On January 1, 2020, the United States Department of Defense (DoD) released its Cybersecurity Maturity...
5 Best Practices for Securing Modern Web Applications and APIs
Web applications are nothing new. Neither is web application security. Many businesses have been building...
Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another security breach. Ponemon Institute has found that the typical...
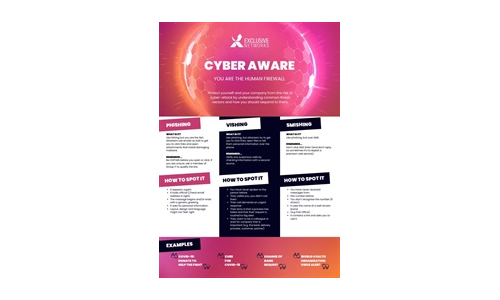
Cyber Aware Infographic
Download this Infographic to see how you can protect yourself and your company from the risk of cyber-attack...
Proofpoint Information and Cloud Security Platform
The Proofpoint Information and Cloud Security platform combines many of our products to address secure...
MSP Security Best Practices: Ransomware Attack Prevention
In Datto's Global State of the Channel Ransomware Report, 4 in 5 managed service providers (MSPs) agreed...
10 Key Questions to Include in Your Vendor Security Questionnaires
Today's perilous cyber world requires you to carefully check your vendors' security posture – typically...
6-Step Cybersecurity Starter Guide for SMBs
Computers and the internet bring many benefits to small businesses, but this technology is not without...

CRM Evolved Introducing the Era of Intelligent Engagement
Digital Transformation, a key focus of successful organizations, proves itself a business imperative,...

Zero Trust Privilege for dummies
Cyber breaches are bigger and worse than ever. Hardly a day goes by without headlines about some new...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.